EGERIE Risk Manager
Planck
Streamed Access Management: The Dawn of Intent-Aware Access
Cyber Trust Label
The Cyber Trust Label shows that you are a secure and trustful organisation within the supply chain...
Trakia Cyber Range
Digital Innovation Hub Trakia builds and offers free-of-charge a Cyber Range as a Service solution...
Secfense User Access Security Broker (UASB) | Switch to MFA, FIDO2 or Passkeys in 5 minutes
The Secfense User Access Security Broker streamlines the adoption of multi-factor and FIDO2...
Secfense IdP (Identity Provider) | Secure, flexible and simplified identity management
Secfense IdP marks a significant advancement in cybersecurity, delivering unparalleled flexibility...
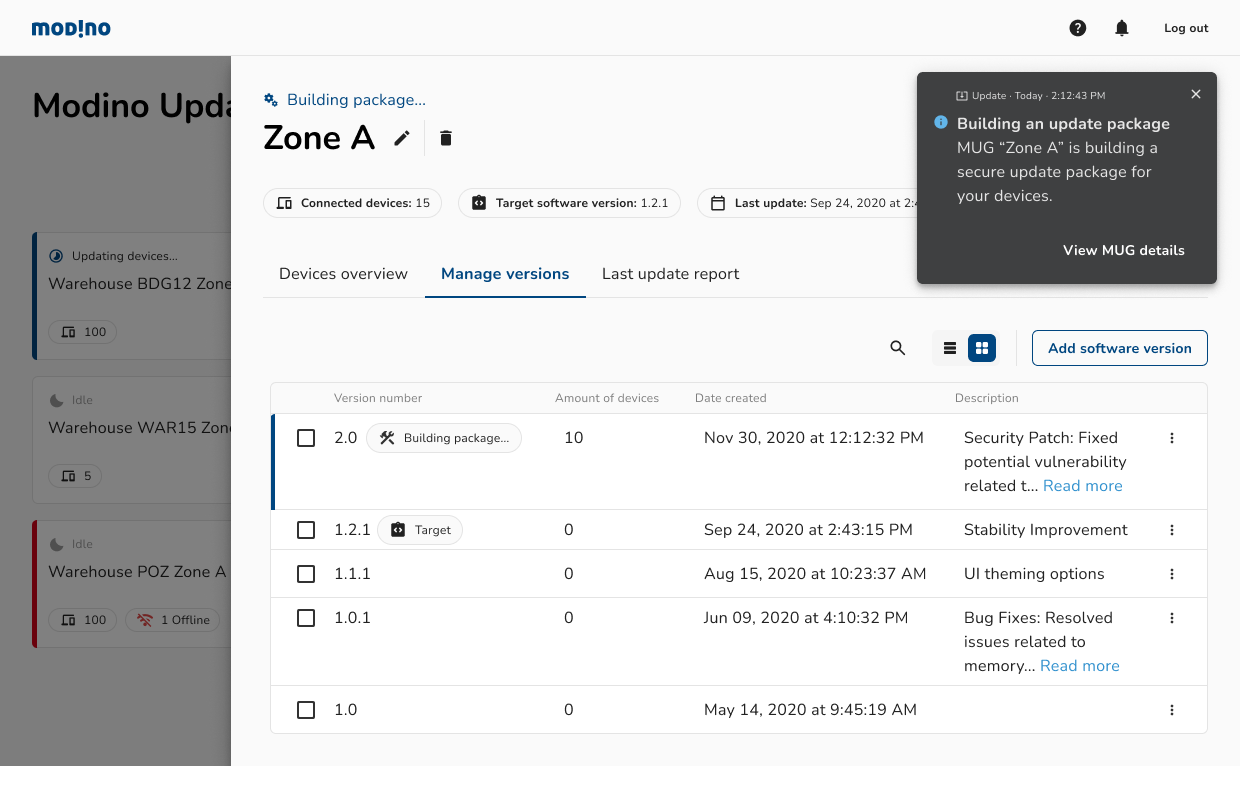
Modino.io - safe and secure digital artifacts delivery
Modino.io is an on-prem / cloud platform for performing safe and secure updates for: - IoT devices -...
Threema Work. The Secure Business Messenger
Threema Work is a secure and GDPR-compliant business communication solution that facilitates mobile...
Binalyze AIR
Binalyze AIR is an investigation and response automation platform powered by forensic-level...
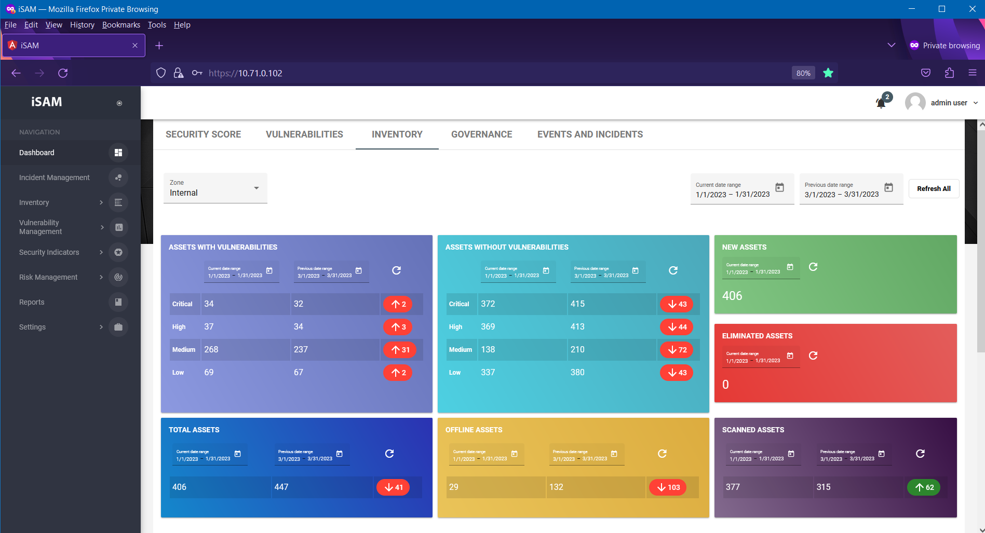
iSAM - Information Security Automation Manager
iSAM is a product developed by Safetech Innovations, in order to ensure automation in the...